Why Fingerprint Devices Are Essential in Today’s Digital India
🚀 Why Fingerprint Devices Are in High Demand
1. Government Integration
With initiatives like Digital India and Aadhaar-based services, biometric authentication is mandatory in many sectors.
2. High Security
Fingerprints are unique, making them one of the most secure methods of identity verification.
3. Fast & Efficient
Compared to manual verification, fingerprint devices complete authentication within seconds.
4. Easy to Use
Plug-and-play devices with simple software integration make them user-friendly for businesses.
🏢 Use Cases for Businesses
Fingerprint devices are essential for:
- CSC & e-Mitra centers
- Banking correspondents (BC)
- Retail shops doing KYC
- Corporate attendance tracking
- Telecom retailers
⚙️ Types of Fingerprint Devices
There are mainly two types available in the market:
- L1 Devices – Used for secure Aadhaar authentication
- L0 Devices – Used for basic biometric applications
Businesses should choose the device based on their usage and compliance requirements.
🛒 Choosing the Right Device
Before purchasing, consider:
- RD Service compatibility
- Build quality & durability
- Support & warranty
- Software integration
- Certification (UIDAI approved)
💼 Why Buy from a Trusted Supplier
Buying from a reliable supplier ensures:
- Genuine products
- Proper guidance
- After-sales support
- Quick service in case of issues
🤝 About Dhairya Enterprises
Dhairya Enterprises has been serving customers across India since 2010, providing high-quality biometric devices, 4G dongles, Android TV boxes, and computer accessories.
With a strong focus on trust, support, and genuine products, the company has successfully served 10,000+ customers nationwide.
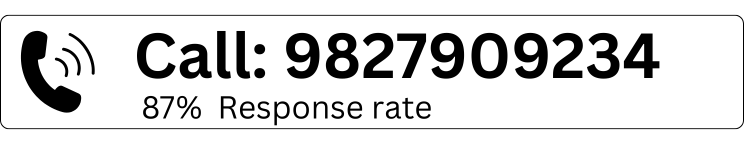
📞 Contact Us
For the best deals and support:
- Call: 9584450043
- WhatsApp: 9827909234
- Website: dhairyaenterprisesindia.com
🔚 Conclusion
Fingerprint devices are no longer optional—they are essential tools for modern businesses. Whether you are running a CSC center, a retail shop, or a banking service, investing in a reliable biometric device will improve efficiency, security, and customer trust.







Add comment
You must be logged in to post a comment.